Example for Configuring Authentication for Telnet Login Users (Using the Secure ACS as a RADIUS Authentication Server) - S600-E Series Switches Typical Configuration Examples - Huawei

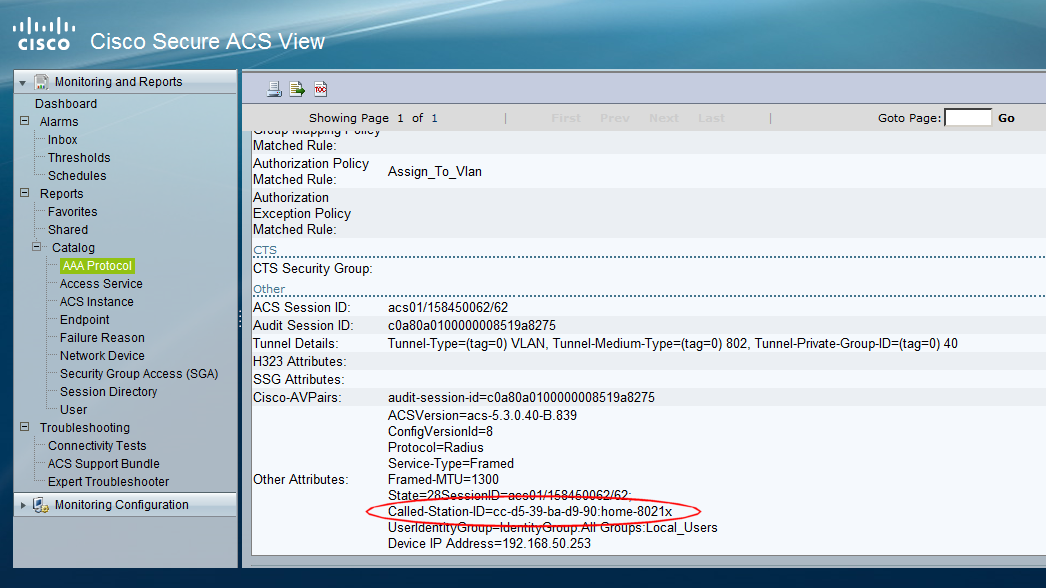
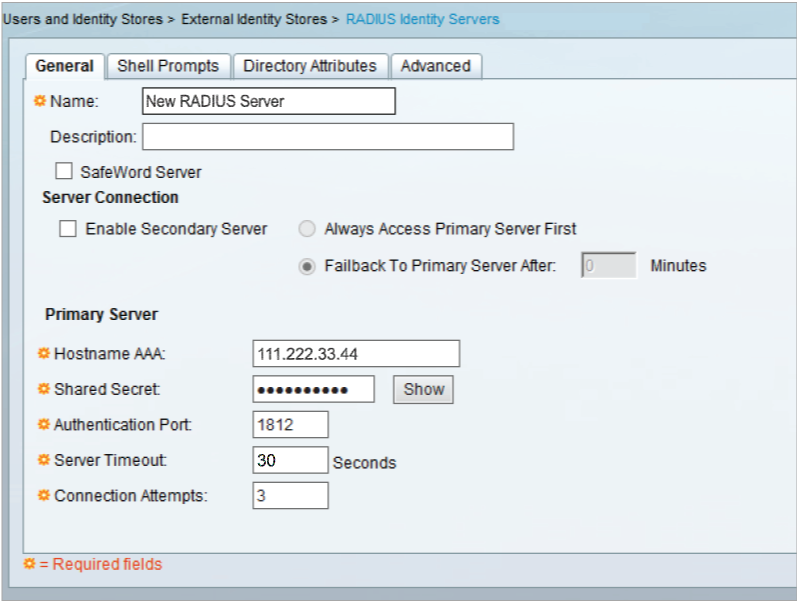
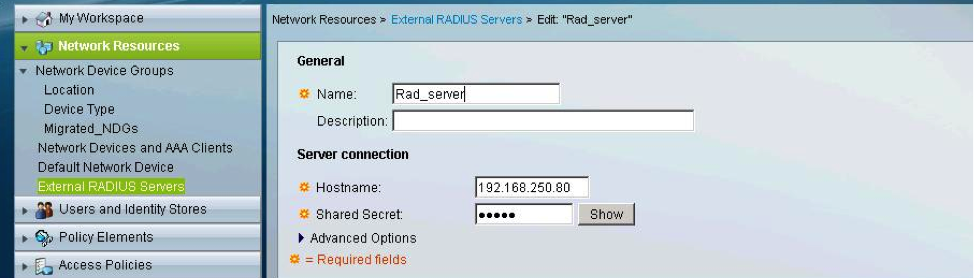
The Cisco Secure ACS and its configuration. The AP was configured to... | Download Scientific Diagram